
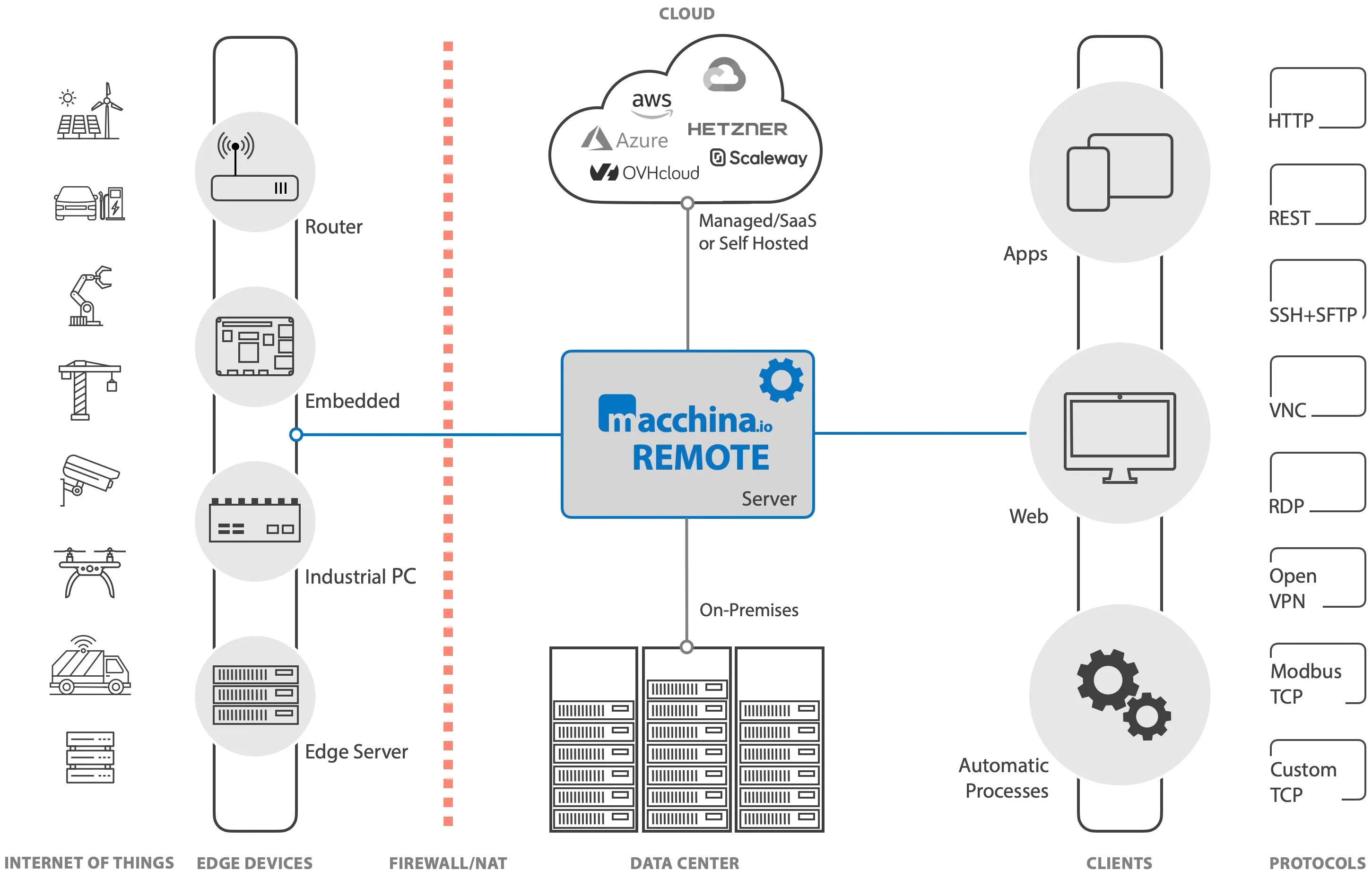
macchina.io REMOTE provides secure and transparent remote access to the built-in web server of an IoT or edge device, or any machine on a private network behind a NAT router or firewall. Access the web interface of your device from anywhere using any web browser.

macchina.io REMOTE allows mobile apps to securely talk to REST APIs on remote IoT devices. Or remotely access TCP-based industrial protocols such as Modbus-TCP and OPC-UA on the shop floor, from desktop applications or cloud services.

macchina.io REMOTE provides secure remote forwarding of TCP-based protocols, including SSH, SFTP, VNC and RDP, for secure remote management, user assistance, troubleshooting and debugging.
The internet has become a dangerous place for devices. With macchina.io REMOTE, you don't have to expose your device to the internet using a public IP address or port forwarding on a NAT router. Your device can stay behind a firewall or router, and you can exactly control who is allowed to access it remotely (RBAC and 2FA) - leaving zero direct attack surface. Of course, all communication between your device and macchina.io REMOTE is encrypted with TLS.
A remote access solution with macchina.io REMOTE can be set up in less than one hour. The macchina.io REMOTE server can run on premises or on a virtual machine in the cloud, native or in a container - it's your choice. The macchina.io REMOTE device agent can be easily integrated into Linux-based devices or gateways, or can run on a Windows, macOS or Linux machine in the same network as the device. No changes to the network infrastructure are required in order to access the device.
macchina.io REMOTE provides secure remote access for your in-house support staff, external service partners, or end users. A powerful user management and permissions system controls who has access to which devices. Besides providing remote access for customer assistance, support, servicing and trouble-shooting, macchina.io REMOTE greatly simplifies integration of mobile apps or AI assistants with your devices.
The macchina.io REMOTE web user interface can be highly customized to fit your device design
and branding. Plug-ins, REST APIs and webhooks allow deep integration with your own applications and systems.
Deploying a remote access solution based on macchina.io REMOTE is much more cost effective
than rolling your own solution.
The EU Cyber Resilience Act demands that you secure, patch, and monitor your connected products for their entire lifecycle. macchina.io REMOTE is the remote access layer that makes this possible — with SSH, VNC, RDP, HTTP, and SFTP tunnels to devices behind any firewall.
Sanctions, policy shifts, service outages, new terms of service — when your remote access depends on a provider outside your jurisdiction, your product's lifecycle depends on decisions you can't influence. macchina.io REMOTE is built and operated in the EU, self-hostable on your own infrastructure, and designed so that no external actor can switch it off.
The tunnel connections between device and macchina.io REMOTE server and also the connection between client (web browser) and macchina.io REMOTE server are secured using TLS. Furthermore, your devices are never exposed directly to the internet — they can safely stay behind a firewall or router, leaving zero direct attack surface. Access to macchina.io REMOTE can be protected with two-factor authentication (2FA) using time-based one-time passwords (TOTPs).
Through a secure tunnel to the macchina.io REMOTE server the edge device becomes just another host on the internet, addressable via its own URL and protected by macchina.io REMOTE against unauthorized or malicious access. No public or static IP address is required for the device.
The macchina.io REMOTE server typically runs on a virtual Linux server or in a container. It can be deployed on cloud platforms such as AWS, Azure, OVH or Hetzner, or on-premises. Multiple instances can be run in a load-balancing setup if required to reliably handle a very large number of simultaneously connected devices and user sessions. Metrics are exposed via a Prometheus/Open Metrics interface.
macchina.io REMOTE can be easily customized and extended via plugins to customize the user interface or add customer-specific features. It optionally supports LDAP for user authentication and provides REST APIs and webhooks for integration with customer-specific or third-party applications.
macchina.io REMOTE does not require a VPN. Devices connect to macchina.io REMOTE using a TLS-protected WebSocket connection. This connection is then used for tunneling TCP connections to the device. Therefore, macchina.io REMOTE is the perfect solution in situations where a VPN cannot be used for technical or legal reasons, or where a VPN simply does not fit the requirements, e.g. if fine-grained access control is needed.
macchina.io REMOTE works with home automation devices, monitoring and control systems for green energy facilities, remote automation and data acquisition devices, data loggers, device servers, IoT gateways, POS systems, IP cameras and network video recorders, telecommunication equipment, industrial automation systems (PLCs), remote edge computing infrastructure, or any other connected device. The device agent is available for multiple operating systems and hardware architectures.
macchina.io REMOTE supports flexible users and permissions management, including role-based access control (RBAC), via its web application, the REST API, or a command-line interface (CLI). This allows very fine-grained control of which users may access which devices (and which ports). For example, an end user may only access their own device, wheres service partners may access all their customer's devices. Or some users can only access the web application of a devices, and some may connect via SSH too.
The REST API provides full access to all device management features of the reflector server. Using the REST API, devices can be created and deleted, device properties can be retrieved, modified, added and deleted, and available devices can be queried. There is also a REST API for managing users and their roles and permissions (role-based access control).