Remote Access: The Pros and Cons of Virtual Private Networking
Secure remote access to IoT edge devices is one of the fundamental requirements of the Internet of Things. IoT devices are often located in places that cannot be reached easily by support technicians, such as remote locations or factory floors with access restrictions. Nevertheless, it must be possible for support staff and other authorized staff to get access to devices in the field for troubleshooting, maintenance and customer support.
 Garden Wall Weather Station; Photo Credit: USGS, Flickr, Public Domain
Garden Wall Weather Station; Photo Credit: USGS, Flickr, Public Domain
Remote Access Use Cases
Generally, there are different remote access use cases that need to be supported. They can be split into who needs to access the device, and how the user interacts with the device. First, who may need to remotely access a device:
- The device manufacturer’s support team
- Device software developers, during field tests
- Service providers or sales partners of the device manufacturer
- End users
The device manufacturer’s support team needs access to deployed devices to troubleshoot issues, update configuration settings or install software updates. Similarly, developers may require remote access to devices during early field tests, if devices are located in remote or otherwise not easily accessible locations (e.g., a customer’s plant).
Service providers need access to their customer’s deployed devices, also for troubleshooting, maintenance and support purposes.
Finally, end users want to remotely access their devices, often via a mobile app.
Second, there are different ways to interact with the device:
- Web-based user interface
- Mobile app
- Graphical user interface
- Command line interface shell
Many IoT edge devices provide a web-based user interface for configuring, managing and operating the device. Some devices also come with a smartphone app for the same purpose. Communication between app and device is often done with a REST API implemented on the device. Devices with a touch screen run some kind of graphical user interface. And finally, a command-line shell is available as well, specifically on Linux-based devices.
Some kinds of devices have no means of direct user interaction. These devices usually connect to a server to receive configuration updates or commands.
Remote Access, But Secure
IoT edge devices are often connected to private networks behind NAT routers or firewalls. Even devices connected to mobile networks such as 3G or LTE in most cases do not have public IP addresses and thus are not directly reachable over the internet. This means that while these devices can open connections to servers on the internet, it is not possible to access the device’s web server from the outside, unless additional measures are taken. This is generally a good thing. Exposing edge devices directly to the internet opens the door to vulnerabilities and various kinds of attacks.
Setting up port forwarding on a NAT router together with Dynamic DNS, or exposing a device directly to the internet via a public IP address is in most cases a very bad idea. Such devices can be easily detected via specialized search engines such as Shodan, or via brute-force port scans. The recent history is full of examples where devices such as IP cameras or routers have fallen victim to cyberattacks. Exploiting insecure default passwords, or even open telnet (or other network services) ports without any authentication at all, along with vulnerabilities in embedded web servers and web applications, are common threats. Such devices often end up in botnets, used for wide-scale distributed denial-of-service (DDoS) attacks such as Mirai, or are used for crypto-currency mining.
VPN for Remote Access to IoT Devices
Virtual Private Network (VPN) technology is often used to implement remote access to IoT edge devices in a secure way. Typically, the IoT device contains a VPN client that connects to a cloud-based or on-premises VPN server. The device is directly integrated into a remote network using a secure, encrypted tunnel through the internet. VPN technology is widely available, and open source implementations such as OpenVPN can be easily obtained.
However, VPN technology has a number of characteristics that make it unsuitable for some remote access use cases. Generally, in order to connect to a device, a user must be in the same network that the devices are connected to via VPN, or in a network connected to the VPN network. This restricts the practicability of VPNs for use cases where users from different organizations (such as service partners or end users) should be able to get access to devices. Specifically, users connected to the VPN must be restricted from accessing devices they are not authorize to access. Furthermore, it would be a good idea to prevent devices from seeing and connecting to other devices in the VPN. Otherwise, a compromised device could easily be used as an entry point to attack other devices in the same VPN.
While not impossible, this requires a lot of extra efforts when setting up a VPN. Nevertheless, for providing end users remote access to their devices, VPNs are unsuitable, as end users cannot be expected to set up VPN connections from their client systems such as PCs, smart phones or tablets.
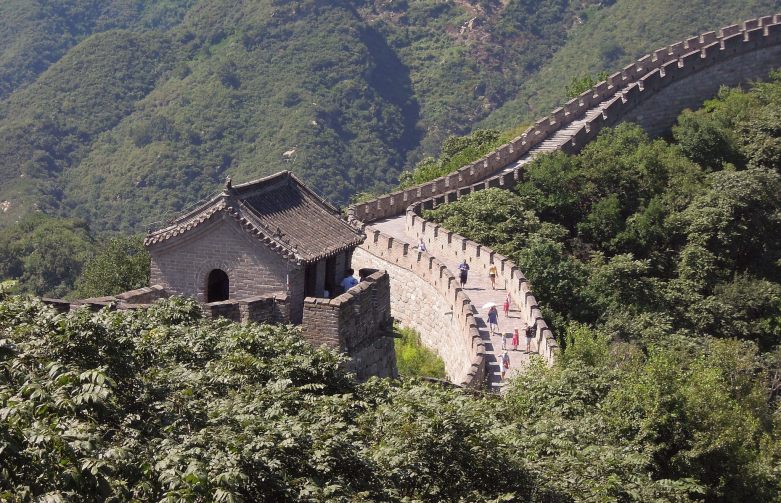 Great Wall of China; Photo Credit: Güldem Üstün, Flickr, CC BY 2.0
Great Wall of China; Photo Credit: Güldem Üstün, Flickr, CC BY 2.0
There is yet another important restriction to VPNs. If your devices are located in China, a VPN solution is most certainly out of question. Recent legislation in China severely restricts VPN connections from within mainland China to foreign servers. VPNs have been very popular vehicles to circumvent China’s Great Firewall and the government’s internet censorship, and therefore have been severely restricted (to a few authorized providers) as of early 2018.
Macchina.io Remote Manager – A Great Alternative to VPN
macchina.io Remote Manager enables easy and secure remote access to the web server and other TCP-based services such as secure shell (SSH) or remote desktop (VNC) of a device, even if the device is located in a private or mobile network behind a NAT router or firewall.
Remote Manager uses a HTTPS-based tunneling protocol based on WebSockets. A connector application (WebTunnelAgent) running either directly on the device, or on another device in the same network (a router, gateway or desktop system) opens a WebTunnel connection to the reflector server. The reflector server then uses this tunneling connection to send HTTP requests or other TCP protocol payloads to the device.
Remote Manager supports the most commonly used protocols for connecting to the device. Beside HTTP, SSH and VNC (remote desktop) connections are supported. A web-based VNC client is even integrated into the Remote Manager web user interface. This greatly helps in remote assistant scenarios, where a support agent needs to access the graphical user interface of a customer’s device. With the help of a client application, virtually every TCP-based protocol can be securely tunneled from a client device to the remote device.
Since the device actively opens the connection to the Remote Manager server, NAT routers or firewalls do not block the connection. Furthermore, the WebTunnel protocol is based on the standard WebSocket protocol, which again is based on HTTP. This makes the connection work even across a HTTP proxy server. Even a firewall is less likely to block the connection.
Remote Manager also enables remote access via mobile iOS and Android apps. The REST API of a device that is typically used for communication between app and the device can be exposed to authorized users via Remote Manager. This removes the need of creating a custom server application in order to enable app-based remote control for IoT devices.
Remote Manager is a proven and cost efficient solution for providing secure remote access to IoT edge device for support staff, service partners and end users.
To learn more about Remote Manager:
- Download and read the White Paper: Web-based Secure Remote Access to IoT Edge Devices
- Sign Up for a free Remote Manager account
- Get started with a Raspberry Pi
